Learn what Certificates as a Service stand for, discover why Code Signing certificates are a precious commodity and find out how to protect yourself online.
A recent phenomenon tracked by IBM Security X-Force researchers is the CaaS (Certificates as a service). Cybercriminals would use the Dark Web for selling high-grade code certificates -which they have obtained from trusted certificate authorities- to anyone that is interested in purchasing them.
Sales of code signing certificates have increased considerably over the past few months, according to X-Force researchers who have also provided some best practice guides on checking for trusted certificates.
Talking about certificates
Why were certificates created? Their purpose is to generate trust and validation in software of code run on the machines. Using certificates, we can be safe about things like that a file has arrived from a valid source, it is not tampered with and its origin is open so we can validate its publisher.
Who issues the certificates and to whom are they granted? They are issued by the certificate authorities (CAs) and are granted to companies that generate code, protocols or software so they can sign their code and indicate its legitimacy and originality.
Talking about the importance of the certificates
Using code signing certificates is similar to the hologram seal used on software packages, assuring they are genuine and issued from a trusted publisher. Users would receive alerts in an attempt to install files that are not accompanied with a valid certificate.
This is why cybercriminals aim to use certificates for legitimizing the malware code they make.
Cybercriminals using signed malware
When cybercriminal create malicious code, their purpose is to make it appear as legitimate as possible. This is done by using signing certificates to sign their code.
By stealing private keys of certificates using Trojan horses or by compromising the certificate key builder of software vendors, cybercriminals manage to get access to code signing certificates.
Suspicious certificates
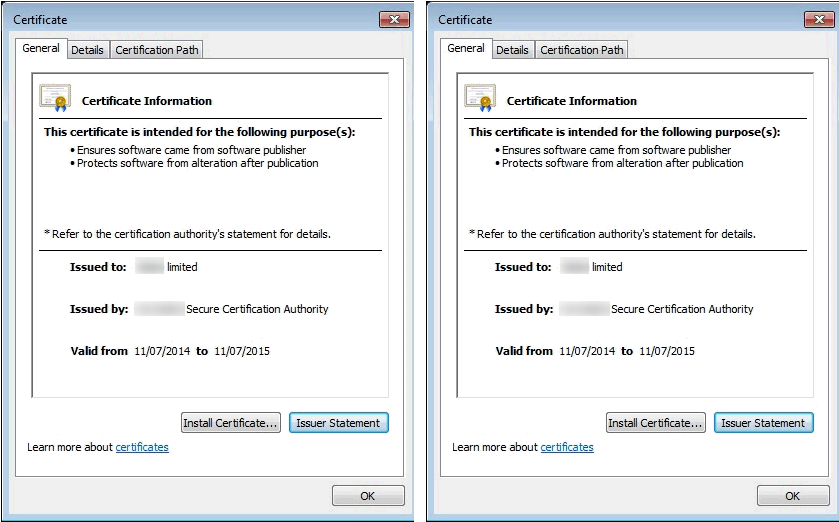
When the researchers discovered that fraudsters used valid certificated, the first thing that came to their mind is that they somehow manage to acquire them directly from the certificate's issuer. What they did next is that they contacted the certificate owner, advised that it has been stolen and offered up to cybercriminals.
It is quite possible that cybercriminals would use certificates to register dummy corporations and then issue bank accounts, checks etc. It can be rather difficult to separate legitimate from dummy companies and this is due to the fact that cybercriminals take all the required steps for making it appear as authentic.
Recommendations
New measures of verification that will keep intruders away and not block code from legitimate vendors are needed.
Here's what you can do:
- Keep your operating system and the installed browsers fully updated.
- Do not add any new CAs to the root certificates zone (unless you are a security professional).
- Ban any files issued by unknown developers.Check the validity of the certificates and verify additional attributes like the certificate's hash sum.
- Keep a list of trusted certificates and update it regularly (a task for system administrators).
- Deploy endpoint security solutions.


