The websites based on the popular Joomla CMS need to be updated as soon as possible due to a critical remote code execution vulnerability.
The websites based on the popular Joomla CMS need to be updated as soon as possible, Joomla has just released a security patch to fix a critical eight-year-old remote code execution vulnerability. The critical flaw was already exploited in the wild, during the weekend experts at the Sucuri firm observed an alarming increase in the number of attacks.
According to the security expert Daniel Cid from Sucuri, starting from Saturday hundreds of attacks are now taking place.
"What is very concerning is that this vulnerability is already being exploited in the wild and has been for the last 2 days. Repeat: This has been in the wild as a 0-day for 2 days before there was a patch available." States the blog post published by Sucuri.
"The wave of attacks is even bigger, with basically every site and honeypot we have being attacked [which] means that probably every other Joomla site out there is being targeted as well."
The zero-day flaw could have a significant impact on the Internet users considering that Joomla is the most popular content management system having been downloaded more than 50 million times.
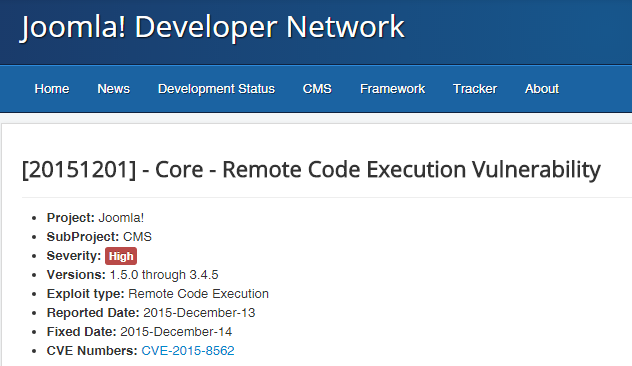
According to a security advisory published by Joomla, all versions above 1.5 are affected. It is important to update the CMS version to the patched version 3.4.6.
"Browser information is not filtered properly while saving the session values into the database which leads to a remote code execution vulnerability," it says.
Sucuri is inviting users to protect their websites and looking for possible indicators od compromise. The attackers are running object injection through the HTTP user agent with exploits from the IP address 74.3.170.33, 146.0.72.83, and 194.28.174.106.
"If you are a Joomla user, check your logs right away. Look for requests from 146.0.72.83 or 74.3.170.33 or 194.28.174.106 as they were the first IP addresses to start the exploitation. I also recommend searching your logs for "JDatabaseDriverMysqli" or "O:" in the User Agent as it has been used in the exploits. If you find them, consider your Joomla site compromised and move to the remediation / incident response phase." States Sucuri.
Don't waste time, check log and update your Joomla version asap.


