The Director of the Tor Project Roger Dingledine has accused the FBI of commissioning to the Carnegie Mellon boffins a study on methods to de-anonymize Tor users.
The experts at the Tor Project have collected more information about the attack launched last year by Carnegie Mellon researchers on the popular anonymizing system.
The Director of the Tor Project Roger Dingledine has accused the FBI of commissioning to the Carnegie Mellon boffins a study on methods to de-anonymize Tor users. The FBI has paid at least $1 million track Tor users and to reveal their IP addresses as part of a large criminal investigation.
"Apparently these researchers were paid by the FBI to attack hidden services users in a broad sweep, and then sift through their data to find people whom they could accuse of crimes. We publicized the attack last year, along with the steps we took to slow down or stop such an attack in the future:
https://blog.torproject.org/blog/tor-security-advisory-relay-early-traffic-confirmation-attack/
We have been told that the payment to CMU was at least $1 million." reads a blog post published by the Tor Project.
In 2014, researchers from Carnegie Mellon University's computer emergency response team (Cert), Alexander Volynkin and Michael McCord, announced that they were able to de-anonymise Tor users and planned to reveal their discovery during the next Black Hat Conference in August.
A few weeks later the organization of the BlackHat had been contacted by the university's lawyers which informed it that the researchers will not participate in the event.
"Unfortunately, Mr Volynkin will not be able to speak at the conference since the materials that he would be speaking about have not yet [been] approved by Carnegie Mellon University/Software Engineering Institute for public release," states the message posted on the official website of the event.
The experts at the Tor Project are accusing the FBI of an attack on a large scale, the researchers confirmed that the offensive launched by the experts at the Carnegie Mellow University was not narrowly tailored to target specific individuals charged of criminal activity.
The attack represented a clear violation of trust and basic guidelines for ethical research.
"We strongly support independent research on our software and network, but this attack crosses the crucial line between research and endangering innocent users." continues the post.
Neither the FBI not Carnegie Mellon representatives commented the accusation, Ed Desautels, a spokesman for Carnegie Mellon's Software Engineering Institute only told Wired that he was not aware of any research activity commissioned to his institute.
"I'd like to see the substantiation for their claim," said Ed Desautels. "I'm not aware of any payment."
The evidence of the collaborations between the FBI and the Carnegie Mellon University has emerged also in a stand trial in federal court in Seattle later this month. The court was discussing the case of Brian Farrell, an alleged Silk Road 2 lieutenant, the law enforcement discovered the IP addresses belong to the suspect. A new filing in Farrell's case states that a "university-based research institute" supported the investigation and helped the feds to de-anonymize Farrell.
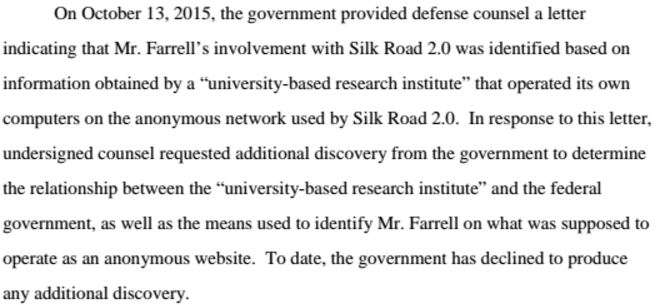 According to a Homeland Security search warrant, between January 2014 and July 2014 a "source of information" provided law enforcement "with particular IP addresses" that had accessed the vendor side of Silk Road 2.
According to a Homeland Security search warrant, between January 2014 and July 2014 a "source of information" provided law enforcement "with particular IP addresses" that had accessed the vendor side of Silk Road 2.
In July, the researchers at the Tor Project discovered a sustained attack against the Tor Network based on the technique described by the team of Carnegie Mellon University researchers.
"We think it's unlikely they could have gotten a valid warrant for CMU's attack as conducted, since it was not narrowly tailored to target criminals or criminal activity, but instead appears to have indiscriminately targeted many users at once. Such action is a violation of our trust and basic guidelines for ethical research. We strongly support independent research on our software and network, but this attack crosses the crucial line between research and endangering innocent users. This attack also sets a troubling precedent: Civil liberties are under attack if law enforcement believes it can circumvent the rules of evidence by outsourcing police work to universities. If academia uses "research" as a stalking horse for privacy invasion, the entire enterprise of security research will fall into disrepute. Legitimate privacy researchers study many online systems, including social networks — If this kind of FBI attack by university proxy is accepted, no one will have meaningful 4th Amendment protections online and everyone is at risk."continues the post.


