Apple and Microsoft are both taking steps to better explain how they handle customers' personal information. Apple hasn't changed its privacy policy in over a year -- but on Tuesday morning the company updated its website with a fresh explanation of what that policy means, product by product, service by service.
National Encryption Policy draft, everyone is under strict surveillance
The Indian Government plans to release the new National Encryption Policy, a law that seems to be one of the big threat to the Internet freedom.
Gozi Trojan Developer Pleads Guilty
A Latvian cybercriminal who helped in the creation of malware that infected over one million machines globally and resulted in tens of millions of dollars in losses, has pleaded guilty to conspiring to commit computer intrusion.
Six Alleged Users of LizardStresser DDoS Service Arrested in UK
Six individuals have been arrested by British law enforcement as part of an operation targeting those who have used the Lizard Squad's LizardStresser distributed denial-of-service (DDoS) tool.
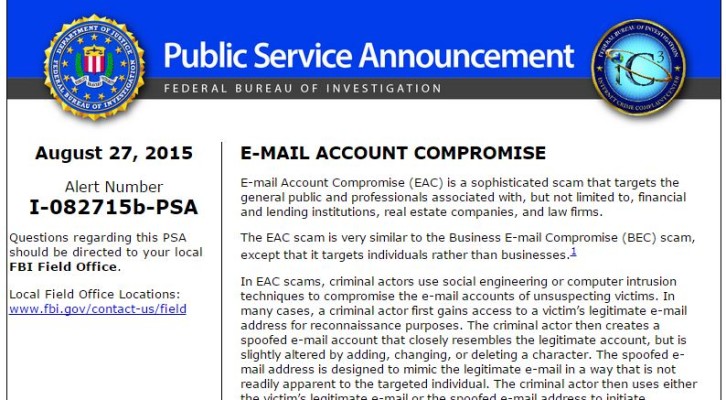
FBI warns that Business Email Scams are raising
Yesterday the FBI warned the world that Business Email Scams (BEC) victims are growing, making companies losing money. The law enforcement highlights that frauds use to start with crooks spoofing communications from high management and executives and deceive them to authorize international wire transfers.
Xkeyscore: the secret Germany’s deal with the NSA
The German weekly Die Zeit disclosed documents that reveal how the German Intelligence did a deal with the NSA to get the access to the surveillance platform XKeyscore.
Russian Lawyers want ban Windows 10 from govt offices
Russian lawyers have filed a complaint calling for restricting the sale of Windows 10 in Russia, the action urges because the newborn OS spy on users violating Russian laws.