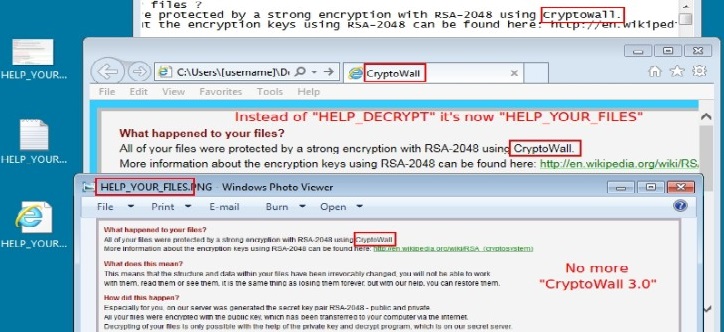
The popular Nuclear Exploit Kit has been used for the first time to serve the ransomware CryptoWall 4.0.
The Nuclear exploit kit is one of the privileged weapon in the arsenal of cyber criminal groups, now the popular crimeware kit has been used to serve the ransomware CryptoWall 4.0. In the past, criminal crews used the exploit kit to serve instances of the CryptoWall 3.0.
The discovery was made by the security researcher at Rackspace Brad Duncan, who explained that it is the first time that the new CryptoWall 4.0 ransomware is spread by using the an exploit kit.
Although Angler may dominate the exploit kit market at this time, the Nuclear exploit kit, arguably the second most prevalent exploit kit found in-the-wild today, has recently been observed utilizing payload delivery mechanisms that are much more efficient and more sophisticated in nature than ever seen before.
One of the primary advances made by the Nuclear Exploit Kit group is that the payloads delivered by the exploit kit are dynamic in nature. While payloads were often rotated during normal Nuclear EK operation, it has been discovered that the payloads delivered by recently-analyzed hosts serving the Nuclear EK have been exceptionally volatile in nature.
The Nuclear EK allows to serve malicious code by exploiting vulnerabilities in Java, Acrobat Reader, Flash, and Silverlight.
The most recent version(s) of the Nuclear EK utilizes effective techniques to evade detection, and even when it fails to exploit a target system, its anti-analysis techniques served to prevent malware analysts from re-creating and following/analyzing the infection chain employed by Nuclear.
Earlier this year, the security expert Maarten van Dantzig discovered a large number of Google ads sold through Bulgarian reseller EngageLab have been redirecting users to websites hosting the Nuclear exploit kit.
Duncan confirmed that samples of the CryptoWall 4.0 ransomware have been spotted in the wild since 2 November.
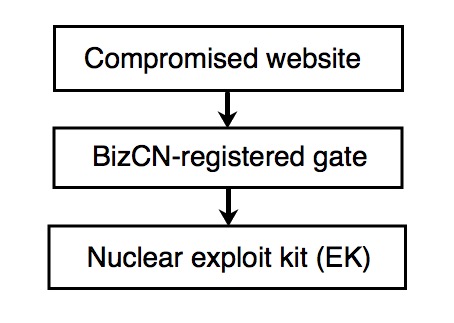
"Earlier this month, the BizCN gate actor switched IP addresses for its gate domains to 46.172.83.0/24. Also, as early as Friday 2015-11-20, this actor started sending CryptoWall 4.0 as one of its malware payloads from the Nuclear exploit kit (EK). Until now, I've only associated CryptoWall 4.0 with malicious spam (malspam). This is the first time I've noticed CryptoWall 4.0 sent by an EK." wrote Duncan. "Until now, I haven't noticed CryptoWall 4.0 from any EKs. And now I've only seen it from the BizCN gate actor."
Duncan dubbed the threat actors "BizCN gate actor" because it used domains registered through the Chinese registrar BizCN as a gate to hijack users to the domain hosting the Nuclear Exploit Kit.
"This actor uses dedicated servers for its gate domains. These gate domains tend to stick with one particular hosting provider. At times, the BizCN gate actor will switch hosting providers for its gates, and the IP address block for these gates will change." states Duncan.
Duncan speculates that the disclosure of his analysis will force the BizCN gate actor to change tactics.
"Since this information is now public, the BizCN gate actor may change tactics. However, unless this actor initiates a drastic change, it can always be found again. I (and other security professionals) will continue to track the BizCN gate actor. Expect another diary on this subject if any significant changes occur."
In order to protect your PC keep your software up to date.