A group of researchers from the iTrust has demonstrated how to use a Drone to intercept wireless printer transmissions from outside an office building.
Recently I wrote a blog post on the Infosec Institute titled "Modern Physical Security Awareness Is More Than Dumpster Diving" where I explain how the concept of physical security is evolving with technology. In particular, I have also focused the analysis on the threat represented by drones, these vehicles, in fact ,can easily bypass conventional physical defense systems and hit a target in various ways and for different purposes.
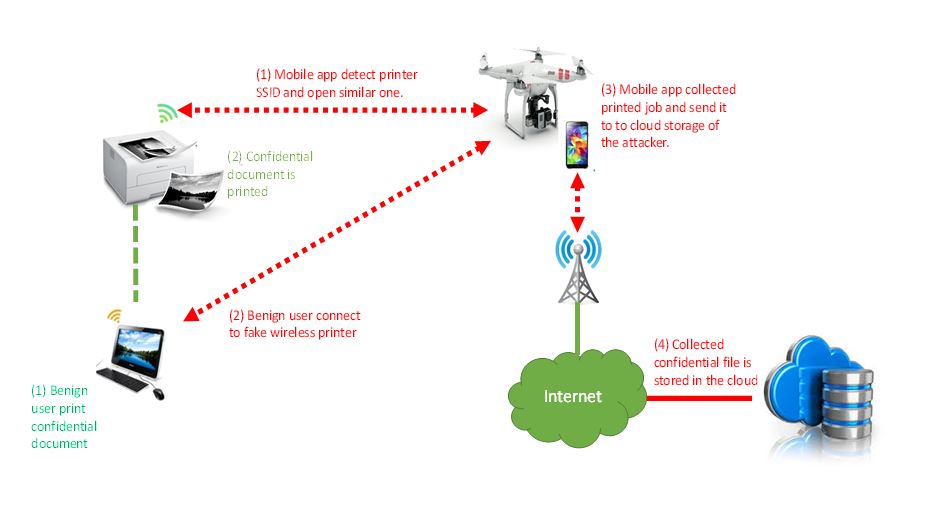
A group of researchers from the iTrust, a research center at the Singapore University of Technology and Design, has demonstrated how to use a Drone to intercept wireless printer transmissions from outside an office building. The drone carries a smartphone which runs two custom apps that are capable of intercepting wireless traffic of the printer which contain sensitive data
The researchers accessed a corporate network by using a smartphone-equipped drone to hack internal printers. In the demo provided by the researchers, they use a standard drone from the Chinese firm DJI and a Samsung smartphone.
The researchers have used two applications they have developed:
- A first app that once the open wireless printer is detected, establishes a bogus access point that mimics the printer and tricks computers in the internal wireless network to send sensitive documents to it.
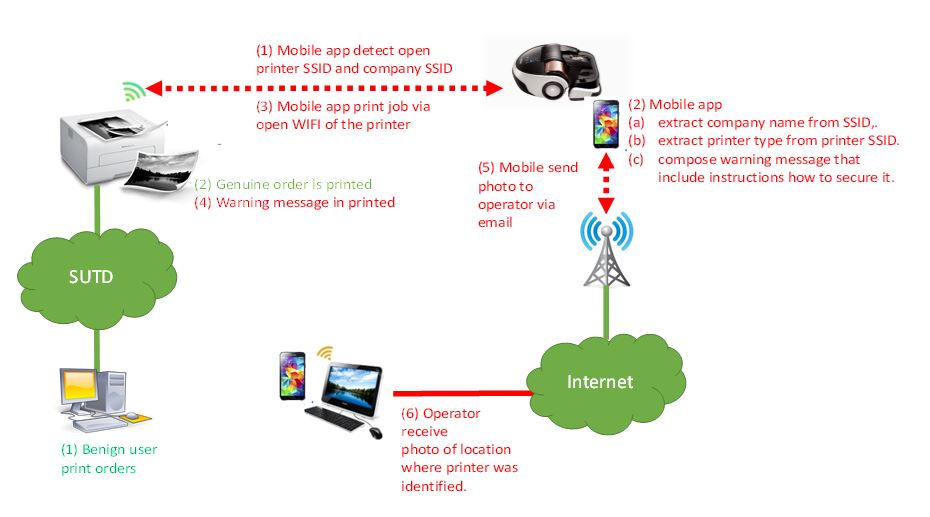
- Cybersecurity Patrol, which was designed to scan the air searching for open WiFi printers and automatically notify the organization's IT department. This app has been designed to improve the security of the target organization. It looks for unsecured printers in the target organization accessible via the drone, but rather launching the attack, it took photos of the compromised printers and report it to the internal staff. "It also sent a print job detailing instructions on how to secure the specific printers that were identified based on their SSIDs."
This attack is very insidious and it is difficult to detect, once a victim's document is intercepted it is sent to an attacker's Dropbox account using the smartphone connection, and it is also sent to the real printer so a victim wouldn't notice the hack.
The researchers presented their hacking technique based on drones to Wired, they explained that an unmanned aerial vehicle could easily bypass physical security measures and cover the area of an entire building trying to hack systems at each floor.
According to researchers, it's quite difficult for one to get to several floors with their devices to hack into networks, but a Drone can do it easily.
""In Singapore ... there are many skyscrapers, and it would be very difficult to get to the 30th floor with your notebook [if there is no] physical access," Yuval Elovici, head of iTrust, a cybersecurity research center at the Singapore University of Technology and Design, explained to Wired. "A drone can do it easily. This is the main point of the research, closing the physical gap with [a] drone in order to launch the attack or scan easily all the organization [for vulnerable devices]."
"After purchasing an HP6830 printer, they reverse engineered the protocol the printer used to communicate with computers sending it documents. Then they rooted a Samsung phone to install the Debian operating system on it. For the app, they wrote some Python code that simulates the HP printer." continues Wired describing the attack.
The researchers have also demonstrated the same attack by using an autonomous vacuum cleaner.
"The researchers also demonstrated the feasibility of this attack from within the building, by hiding the cellphone inside an autonomous vacuum cleaner and having it continuously and autonomously scan the organization's network for printers with unsecured wireless connections." states the blog post published by the experts.
The project conducted by the researchers demonstrate once again the close link between physical and logical security, apparently harmful devices like a vacuum cleaner could be used to penetrate the network of an enterprise.
It's time to approach physical security in a different way!
