A security analyst has demonstrated that WiFi Jamming, such as the Jamming of Bluetooth and Zigbee systems, is very easy and cheaper than ever.
A security analyst has shown that Jamming Bluetooth, WiFi and Zigbee systems is not hard to perform but rather, above all, likewise not as expensive as one may think.
As per Mathy Vanhoef, a PhD understudy at KU Leuven (Belgium), it should effectively be possible by utilizing a Wi-Fi $15 dongle purchased off Amazon, a Raspberry Pi board, and an enhancer that will widen the assault's scope to exactly 120 meters.
The assault would hit all gadgets inside of reach-circle that work in the 2.4 and 5 GHz groups.
With the aforementioned systems being pivotal to the working of numerous IoT gadgets and frameworks – home security frameworks, auto locks, infant screens, etc – it ought to be clear that the way that these assaults can be performed so effectively and efficiently may prompt genuine results.
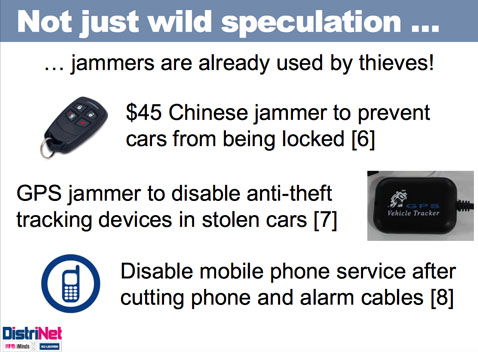
Actually, it is realized that shoddy (very cheap) jammers are as of now being utilized by evildoers around the globe:
 That is the reason it's very crucial that targets have the capacity to recognize these assaults when they are going on, regardless of the fact that they can't stop them.
That is the reason it's very crucial that targets have the capacity to recognize these assaults when they are going on, regardless of the fact that they can't stop them.
Amid his late presentation at BruCON, Vanhoef clarified that by adjusting the dongle's firmware he found himself able to constrain the objective systems to dependably offer need to the gadget's transmissions. On the off chance that the gadget is made to transmit persistently, it implies that every single other gadget won't have the capacity to, making the channel successfully unusable.
His endeavors at particular jamming (blocking particular parcels) have been less effective, and he came to an end that 100% solid specific sticking is unrealistic.
He additionally says that these low-level sticking (jamming) assaults could impact assaults on more elevated amount conventions. For instance, he says that they can be utilized to mount a channel-based MiTM assault against WPA's Temporal Key Integrity Protocol (TKIP), which is still generally utilized.
For those inspired by more subtle elements, here's a video recording of Vanhoef's discussion:
