Stagefright is a nasty potential problem for a huge majority of the World’s Android users. Thomas Fox-Brewster covered it in detail in his article yesterday, but here in brief is how to prevent the bug being used to access your phone without you even knowing.
Stagefright is a core part of the Android OS that is used to handle video and audio. The exploit, which Google has been notified about, will be detailed in full at the Black Hat conference on August 5 and at DEFCON on August 7. If your phone isn’t protected by then, either via an update or through a simple step detailed below then you may well be vulnerable.
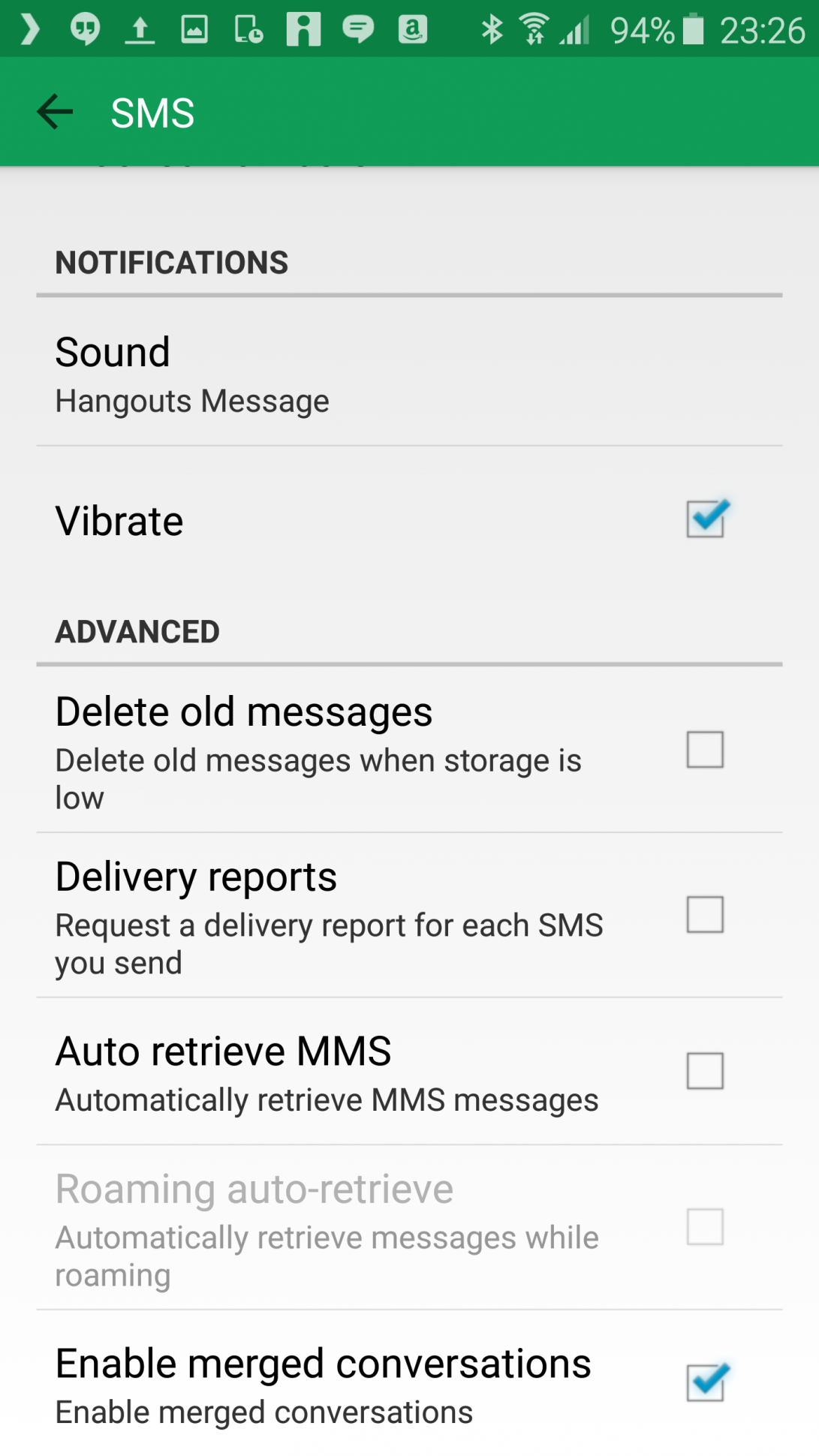
Because the exploit works by downloading code via MMS, to prevent being infected you must go to you SMS settings either in your phone’s SMS app, or through Google Hangouts, whichever you use. There will be an option there to auto-download MMS messages, simply disable it and your phone will not be able to execute the malicious code automatically.
The downsides of doing this are practically none, if you trust someone sending you an MMS you can still get the data, you’ll just be asked each time. Avoid accepting messages from people you don’t know.
There is still a risk involved in you opening the message yourself, but with Google Hangouts the code can be executed without you ever knowing, which is incredibly worrying given that it could then be possible for code to access your phone’s camera and microphone and read data from image folders.
So far it’s not clear what manufacturers are planning updates to take care of the problem. Google has known for a while and while it appears to have fixed certain issues, not all have been addressed. There is some indication here that Android has some problems that allow apps to run with administrative privileges when they shouldn’t. The wider issue though is that with so many different versions of Android and various manufacturer implementations it’s quite hard to tell which devices will potentially be affected.