Microsoft recently fixed the a vulnerability in the Bitlocker disk encryption feature that could be exploited to easily bypassed it is a few seconds.
Stop DDoS attacks in seconds
An Israeli company named "L7 Defense" is trying to do the impossible – to stop application layer DDoS attacks in seconds instead of hours.
The Website of the Norwich airport hacked, a cue to reflect
A hacker shut down the website of the Norwich airport in just a few minutes to demonstrate the importance of a proper approach to the cyber security.
State-sponsored cyberspies inject victim profiling and tracking scripts in strategic websites
Web analytics and tracking cookies play a vital role in online advertising, but they can also help attackers discover potential targets and their weaknesses, a new report shows.
88 percent of company networks vulnerable to privileged account hacks
A research published by CyberArk Labs focuses on targeted attacks against organizational networks, analyzing hackers' methods, tools and techniques.
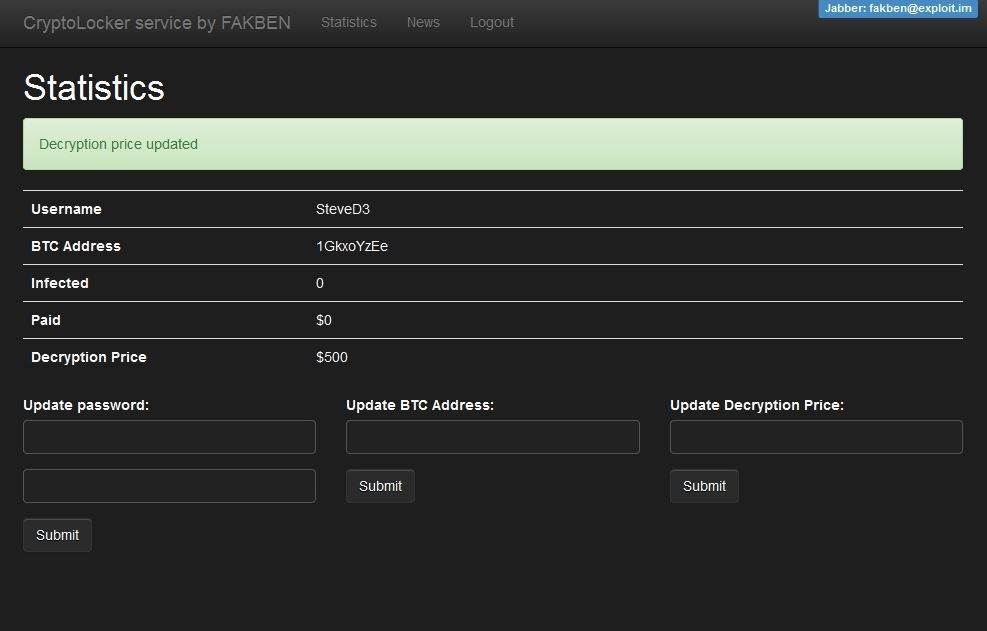
FAKBEN Ransomware-as-a-service emerges from the underground
FAKBEN is offering a professional Ransomware-as-a-service that relies on a new CryptoLocker ransomware which can be downloaded through the executable file.
ProtonMail paid a $6000 Ransom to stop DDoS Attacks
The last few days have not been easy for ProtonMail, the Geneva-based encrypted email service that launched last year.