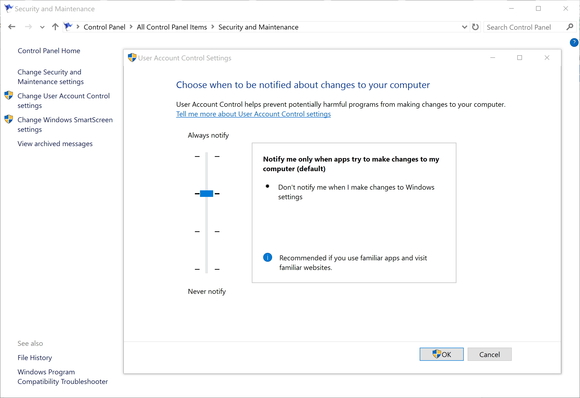
A well-known adware program is preventing users from installing antivirus products by leveraging a Windows feature that was designed for security.
Anonymous Took Down 20,000 pro-ISIS Twitter accounts
In the wake of Paris attacks Anonymous continues its campaign against the ISIS and announced to have taken down 20,000 pro-ISIS Twitter accounts.
Blackhole Exploit Kit Resurfaces in the wild
The experts at Malwarebytes have noticed that threat actors in the wild are reusing the Blackhole Exploit Kit despite its limited effectiveness.
Nested backdoor affects 600,000 Arris cable modems
A Brazilian security researcher has discovered a nested backdoor affecting nearly 600,000 Arris cable modems. Arris is working to fix it.
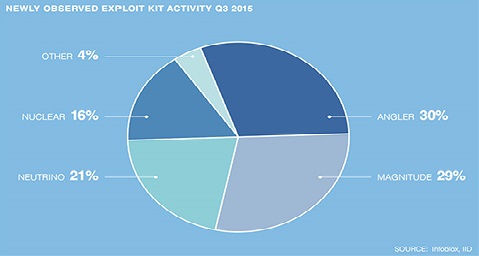
Exploit kit activity up 75 percent in third quarter 2015
In a sign of the increasing professionalization of the space, exploit kit activity increased 75 percent in the third quarter of this year compared to the same period last year, based on DNS activity, according to the latest edition of the Infoblox DNS Threat Index.
The index measures the creation of malicious DNS infrastructure, including exploit kits. Four exploit kits—Angler, Magnitude, Neutrino, and Nuclear—accounted for 96 percent of total activity in the category for the third quarter, reported IID, the company providing data for the index.
Criminals use DNS infrastructure in three ways, according to Rod Rasmussen, president and CTO at IID.
In addition to registering their own, malicious domain names, criminals will also take over legitimate web domain registrations and create malicious subdomains on otherwise safe and well-known websites.
Both the malicious domains and malicious subdomains are pointed to the criminals' own servers, typically located with "bulletproof" hosting providers.
"They're taking advantage of domain registrar security vulnerabilities and adding all these host names, and use the good reputation of a domain name to do evil stuff," Rasmussen said.
There are lists of malicious domains that companies can block, or they can allow access to a white list of domains known to be legitimate. But this security technique fails when the domain itself is a known, good domain, and it's the subdomain that's bad.
Finally, criminals will use DNS lookup requests -- a common and legitimate type of traffic out of enterprises -- in order to exfiltrate stolen data.
"The bad guys know that there's a reasonable chance that the security guys don't have an eye on DNS traffic," said Craig Sanderson, senior director of product management at Infoblox.
The DNS port, Port 53, is pretty much guaranteed to be available, he added. "If I turned off the ability to do a DNS request, you wouldn't be able to go anywhere."
A DNS request isn't normally used to transfer large files, but what criminals do is take their stolen data, and break it up into tiny pieces -- with encryption, if they want, for added protection.
"They can slowly drip-feed the data out," Sanderson said. "Then they reassemble it and decode it."
It takes clever analytics to determine whether a particular message is a legitimate DNS request, or is likely to be a malicious attempt to exfiltrate stolen information.
Another sign of increasing professionalization is that criminals are using the latest software development tools and methodologies, Rasmussen said.
"Before, the exploit kits would be maintained on an ad-hoc basis," he said. "They'd get information about new exploits and do things in batches, once they felt like it."
Now exploit kits are updated with the latest vulnerabilities within days, or even hours, of when they first appear, he said, and the updates are pushed out automatically to the criminal customers.
"They're doing a better job marketing, packaging and keeping their code up to date," Rasmussen said.
Some exploit kits are even distributed in a software-as-a-service model. To keep authorities from shutting down the sites, each customer gets their own domain where the service is hosted.
The buyers use the exploit kits to send out spam, run malvertising campaigns, distribute ransomware, and other nefarious activities.
Damballa finds tools related to the malware that hit Sony
Security company Damaballa said it has found two utilities that are closely related to capabilities seen in the destructive malware that hit Sony Pictures Entertainment last year.
Microsoft touts new, holistic approach to enterprise security
Announcements include Cyber Defense Operations Center that brings together security specialists.