In late 2013, at the height of the holiday shopping season, Target Corporation's point-of-sale payment network was breached, and over 70 million customers had their card payment information stolen, including this author, creating a mass issuing of new cards, limits on purchases for some customers, and various actions by banks who attempted to protect accounts from theft.
After staying quiet for several weeks, Target finally acknowledged the breach a few days before Christmas, causing a loss of several percent in holiday sales. The fallout continued for months with the resignation of the President and CEO, Gregg Steinhafel, and the layoffs of nearly 500 employees. (Clark, 2014) If Target had been the only large retail corporation to be breached with POS malware the story might have died, but others would follow including Neiman Marcus, Michaels, PF Changes, Home Depot, Staples, and others. (Hardekopf, 2015)
The Target fiasco should have been enough to convince other retailers to make immediate changes, but corporations move slowly, and because credit card numbers can be sold on the black market, criminals adapted faster than the corporations. Attacks would adapt and more customers would have their card numbers stolen, thus costing banks and merchants millions of dollars.
How Point-of-sale (POS) Works
To better understand the areas of vulnerability we will review the payment process. For the user of a payment terminal or other payment tool, paying with a debit or credit card feels seamless and simple, but for every payment made multiple parties are involved. Like anything, more entities equal greater risk, and the more access points for a hacker to attack. In a standard card transaction, there is the payment terminal – or Point-of-sale device, then there are one, two, or more banks involved – the issuer, acquirer, and merchant bank. Then there is the payment processing network – most often Visa or MasterCard.
The path that only takes seconds is listed below.
- Customer swipes a card at the merchant
- The Merchant's POS sends the transaction through to the processor
- The Processor encrypts the payment and sends it from the POS device to the payment processing network (Visa, MasterCard, Discover, etc.)
- The payment processing network verifies that funds are available from the card issuing bank
- The card issuing bank then releases the funds back to the processor
- At the end of the day or a sales cycle, the merchant runs a batch with the processor
- The processor then authorizes the release of the funds to the merchant's bank
- Later the customer receives a statement from the card issuing bank noting that funds were removed from a debit account, or that payment is due for credit card purchase.

It is easy to see, from the list above and the simplified transaction process graphic, that there are multiple places for malware to attack or for a criminal using social engineering to manipulate the process.
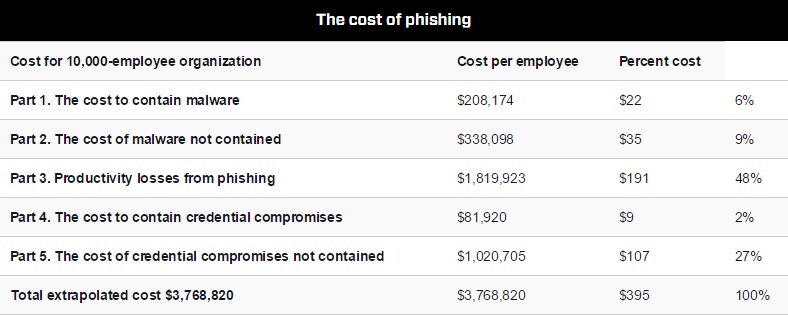
PCI and Payment Safeguards
When a data breach occurs it can cost businesses and banks anywhere from a few dollars per customer to hundreds of thousands to millions for a large breach with thousands of victims. The actual costs vary depending on the source, but whatever the total numbers, the cost is staggering and is costing everyone, including card holders. Target finally figured their losses at $162 million. (Lunden, 2015) The Ponemon research project noted in their 2015 annual study on the cost of a data breach, that the costs were 15% higher than the year before. (Ponemon, 2014) The total estimate cost of credit card theft to banks in 2014 was around 11 billion. (Vlachos, 2015)
Even with the high numbers of breaches it could be much worse if not for payment security standards set by the Payment Card Industry Data Standard (PCC DSS), which is a security standard set by the Payment Card Industry Security Council (PCI SSC). This organization was formed as a partnership between the leading payment companies including MasterCard, Visa, JCB, Discover, and American Express. (PCI, 2015)
The PCI council provides a standard and safety measures for merchants about the security of their payment systems, and it provides a standard for companies providing payment services at any phase of a transaction. The PCI standard has twelve requirements to follow to receive PCI certification. They are:
- Install and maintain a firewall configuration to protect cardholder data
- Do not use vendor-supplied defaults for system passwords and other security parameters
- Protect stored cardholder data
- Encrypt transmission of cardholder data across open, public networks
- Use and regularly update anti-virus software or programs
- Develop and maintain secure systems and applications
- Restrict access to cardholder data by business need-to-know
- Assign a unique ID to each person with computer access
- Restrict physical access to cardholder data
- Track and monitor all access to network resources and cardholder data
- Regularly test security systems and processes
- Maintain a policy that addresses information security for employees and contractors
Current POS Threats
There are multiple and ever evolving threats to the payment landscape. The threats below are only a review, and it is advised that anyone working in payment security watch daily for new vulnerabilities. And it is advised that the security teams protecting point-of-sale networks have a security strategy in place before an attack occurs so that the incident response team can respond quickly.
A common threat is caused by a well-meaning group, the integrators of POS systems. Integrators are companies that manage POS systems by configuring and maintaining the systems. Many small businesses do not have resources or technical skills to maintain their own payment systems, and rely on these integrators to keep their systems running. To access the systems integrators will often use remote access tools like Microsoft Remote Desktop, VNC, and PCAnywhere. These are valuable tools when used correctly, but it has been found that they are sometimes configured incorrectly. This allows for access by cyber criminals who can install malware to steal data and even track keystrokes. (Visa, 2015)
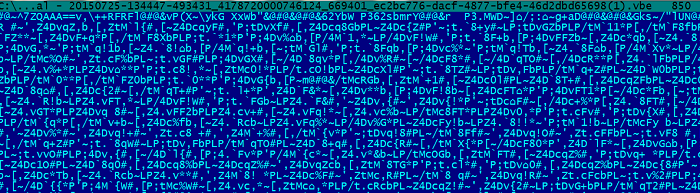
By following the latest PCI standard (PCI-DSS 3.1) known security issues can be mitigated, but if a system is not current malware like RAWPOS can be a threat. This malware is a memory scraper that has infected lodging merchants since 2008. This malware targets the memory dump, where payment information may be temporarily stored, and that data is staged on a network and removed later by a separate process.
The malware used to steal data from infected registers running on Windows at Target was BlackPOS. A few months later, a variant of BlackPOS was used to steal card data from point-of-sale systems at Home Depot. When this memory grabber finds what it's looking for it uploads the data via FTP to a remote server. (Dell SecureWorks CTU TI, 2013)
Chewbacca POS malware is another malware that runs on Windows and scrapes the memory for data. It is not currently widespread. To mitigate Chewbacca POS malware the use of TOR should be prevented and administrative rights should be tightly controlled as administrator permissions are needed to perform the malicious functions of this malware. (Visa, 2014)
A threat that is very simple, and different from the above threats in technology and approach, is the use of skimmers. While these are known to be used at gas pumps and ATMs they can also be used by waiters in restaurants who skim a customer's card out of site of the customer and other employees. By using chip-and-pin technology, and not allowing anyone to take one's card out of site, this crime will be reduced. The new technology will also reduce this crime when magnetic strips with a reusable number are no longer ubiquitous.
As noted above, these are not all of the threats to Pont-of-Sale systems, and new threats are being created daily.
The Chip and Pin Solution
By the end of 2015 a majority of credit cards will be chip-and-pin capable, also known as EMV (an acronym for Europay, MasterCard, and Visa). With the transition to chip-and-pin cards in the U.S. this will become the international standard for securing cardholder data. This is done by using a microprocessor inside of the card. Because of the microprocessor – or chip – the card generates unique data every time the card is used. This is much more secure than the magnetic strip cards we are accustomed to in the U.S. that contain a static number that can be stolen and reused. But, the first generation of chip-and-pin cards will keep the magnetic strip because the transition is not complete.
Starting in October of 2015 the liability will move wholly to the merchant if they do not have chip-and-pin enable terminals, and any banks that haven't issues chip-and-pin cards will be liable if fraud occurs and the terminal is up-to-date. This is to encourage businesses and banks to upgrade their equipment and cards. Magnetic strip cards will still be accepted, but in the next few years these old cards will be phased out.
There are those who believe that chip-and-pin won't stop criminals, and they are correct because criminals will always adapt to the latest technology, and they will always exploit new vulnerabilities. But the new chip-and-pin technology will reduce credit card theft substantially. (Schwartz, 2014) Merchants should always select a vendor that holds the latest PCI certification, as this will reduce many instances of successful POS attacks on their system, but everyone involved must also follow precautions that include being cautious with remote access tools, and maintaining updates and the latest anti-virus software. And, as before, merchants must be vigilant and continue to watch for fake cards and other card scams.
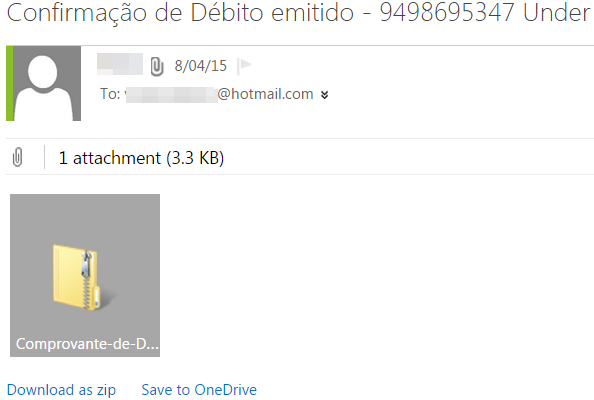
Another step that will improve cardholder security is consumer education. With the introduction of chip-and-pin consumers will be confused. This may be a time of increased social engineering attacks, when criminals attempt to gain the trust of consumers by posing as bankers or other parties that "need" their cardholder information, or worse. Banks and issuers must improve their communication to consumers, and while there have been some efforts, not enough has been done. And, beyond education, as high as 42% of merchants have taken no steps to move to the technology. (Amato-McCoy, 2015) But this author believes that merchants and banks will continue to update to the new technology over the next few years.
Criminals have not stopped robbing banks, despite improvements in security, and criminals will continue to look for vulnerabilities in cards because, like banks, that's where the money is. But, all involved with the processing and issuing of cards must continue to improve security.