Sucuri has noticed a spike in the number of compromised websites as part of a malware campaign which relies on thousands of compromised WordPress sites.
According to security experts at Sucuri, threat actors have hijacked thousands of websites running the WordPress CMS to serve malware.
The technique is not new, legitimate compromised websites host malicious exploits used by crooks to serve malware, they are also being used to redirect visitors to a server hosting the popular Nuclear exploit kit, which is very popular in the criminal ecosystem.
The novelty of this last investigation conducted by Sucuri is that the campaign began 15 days ago, the researchers noticed a spike over the past 48 hours in the number of compromised websites that passed from about 1,000 per day on Tuesday to close to 6,000 on Thursday. On Thursday, Sucuri discovered thousands of compromised sites, 95 percent of which are running on WordPress. The experts are still investigating how the hackers compromised them, they suspect the attackers exploit vulnerabilities in WordPress plugins. Bad news for website administrators, 17 percent of the hacked websites has been blacklisted by a Google service.
![]()
"We are seeing a large number of WordPress sites compromised with the "visitorTracker_isMob" malware code. This campaign started 15 days ago, but only in the last few days have we started to see it gain traction; really affecting a large number of sites.
When victims visit a compromised website, the malicious code it hosts tries a number of different exploits depending on the operating system and available apps running on the device.
"This malware campaign is interesting, its final goal is to use as many compromised websites as possible to redirect all their visitors to a Nuclear Exploit Kit landing page. These landing pages will try a wide variety of available browser exploits to infect the computers of unsuspecting visitors." continues the post.
The security firm has dubbed the campaign "VisitorTracker," because one of the function names used in a malicious code is visitorTracker_isMob().
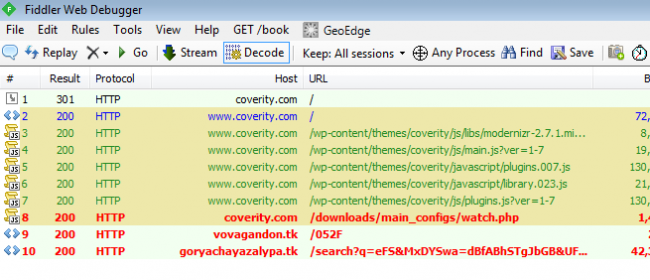
Sucuri researchers discovered that threat actors behind the malware campaign have managed to compromise security provider Coverity and are exploiting it to redirect victims to compromised website.
Sucuri urges administrators to check evidence of the infection on their website, they can use the Sucuri scanning tool to check if their site is affected by this ongoing campaign.


