Joomla just released a patch to fix a critical vulnerability that can allow an attacker to get full administrative access to a website.
The new version of the popular Joomla content management system, the Joomla 3,4,5, is available online. The new release fixes a critical SQL injection vulnerability that could be exploited by attackers to access data in the database of any website running on versions 3.2 to 4.4.4.
The experts also warn about the possibility to combine the flaw with two other vulnerabilities to carry out an attack. There are nearly three million active Joomla instances online that could be potentially compromised by hackers.
The three flaws have been found by the researcher from Trustwave's Spiderlabs Asaf Orpani, who explained that an attacker could hijack the administrator session, exploit the main vulnerability, and then compromise the entire website.
The experts at Joomla fixed the issue in just eight days after their discovery.
The flaw resides in the core module of the Joomla CMS, an attackers can exploit a code from a PHP file in the Adminstrator folder, that is vulnerable to the SQL injection, to steal a session key.
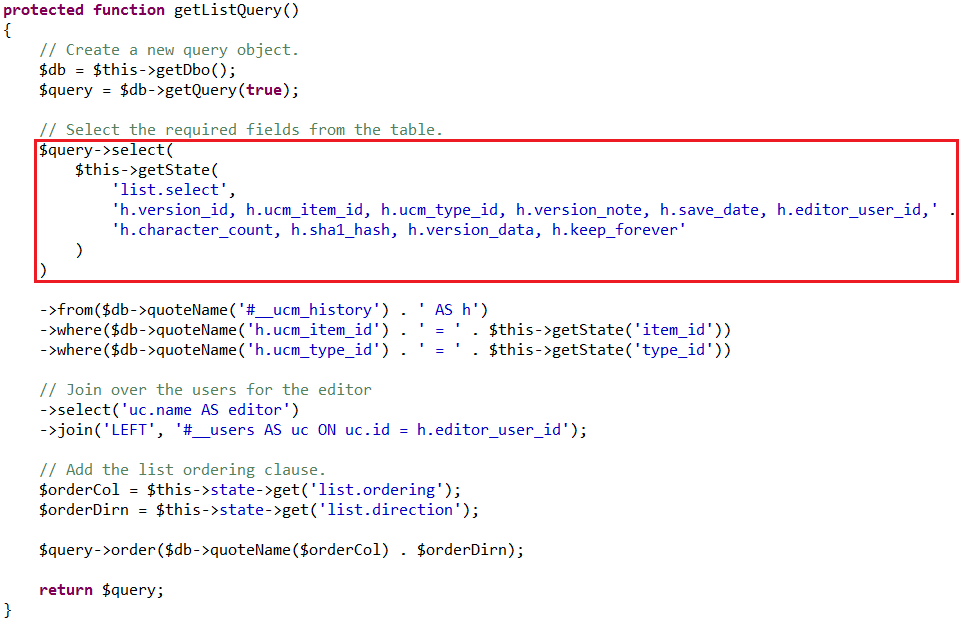 Once obtained the session key it is sufficiently paste it to the cookie section in the request to access the admin folder to obtain administrator privileges.
Once obtained the session key it is sufficiently paste it to the cookie section in the request to access the admin folder to obtain administrator privileges.
"Pasting the session ID we've extracted (which happens to be of an Administrator in our case) to the cookie section in the GET request allows us to access the /administrator/ folder," Orpani writes, "We've also been granted administrator privileges and access to the administrator panel and a view of the control panel. And that's it—we've compromised the website!" the experts wrote in a blog post.
The new Joomla release also addresses two sets of inadequate ACL checks in versions 3.2.0 through 3.4.4, and 3.0 through 3.4.4 of the CMS.