This week Google addressed the concerns about issues raised by information commissioners in ten different countries over privacy and Buzz, while data protection in federal agencies is also a concern.
This week Google addressed the concerns about issues raised by information commissioners in ten different countries over privacy and Buzz, while data protection in federal agencies is also a concern.
Plugged in .. eDemocracy
Samsung Galaxy Store Flaws Can Lead to Unwanted App Installations, Code Execution
Cybersecurity firm NCC Group has shared details on two vulnerabilities in Samsung’s Galaxy Store that could be exploited to install applications or execute JavaScript code by launching a web page.
New House cybersecurity bill
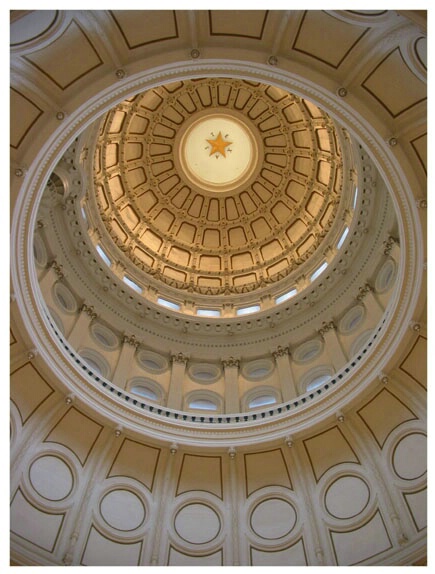 House cybersecurity overhaul included in Defense authorization bill. An amendment to the Defense authorization bill, expected to pass in the House on Friday, would push through committee efforts to update information security requirements for agencies and establish a separate cybersecurity office in the White House.
House cybersecurity overhaul included in Defense authorization bill. An amendment to the Defense authorization bill, expected to pass in the House on Friday, would push through committee efforts to update information security requirements for agencies and establish a separate cybersecurity office in the White House.
APT Hackers Turn to Malicious Excel Add-ins as Initial Intrusion Vector
Microsoft's decision to block Visual Basic for Applications (VBA) macros by default for Office files downloaded from the internet has led many threat actors to improvise their attack chains in recent months.
Rock your boss's world
 CSOs and CISOs should target executive-level management with specially tailored messages that prompt strongly motivated buy-in, even using a bit of fear if necessary, said a panel of state security officials and consultants.
CSOs and CISOs should target executive-level management with specially tailored messages that prompt strongly motivated buy-in, even using a bit of fear if necessary, said a panel of state security officials and consultants.
BitKeep Confirms Cyber Attack, Loses Over $9 Million in Digital Currencies
Decentralized multi-chain crypto wallet BitKeep on Wednesday confirmed a cyberattack that allowed threat actors to distribute fraudulent versions of its Android app with the goal of stealing users' digital currencies.