Experts at Bleeping Computer blog are reporting a new strain of ransomware dubbed LowLevel04 that is spreading via Remote Desktop and Terminal Service.
Crypto researchers: Time to use something better than 1024-bit encryption
It's actually possible for entities with vast computing resources – such as the NSA and major national governments - to compromise commonly used Diffie-Hellman key exchange groups, so it's time for businesses to switch to something else like elliptic curve cryptography, researchers say.
US proposal aims to regulate car privacy, make hacks illegal
A subcommittee of the U.S. House of Representatives has proposed requiring vehicle manufacturers to state their privacy policies, besides providing for civil penalties of up to US$100,000 for the hacking of vehicles.
Phishing websites look more legit with SSL certs from major companies
Netcraft alleges certification authorities aren't properly vetting applicants for SSL/TLS digital certificates
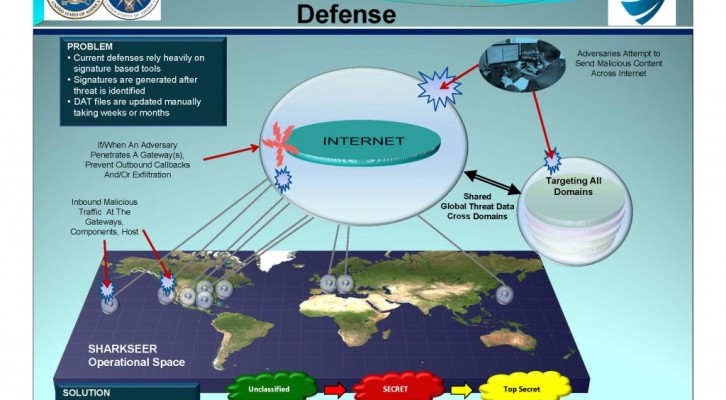
NSA SHARKSEER program aims to detect and mitigate malware Zero-Day
The NSA SHARKSEER Program is a project that aims to detect and mitigate web-based malware Zero-Day and Advanced Persistent Threats using COTS technology.
Code Signing certificates becoming popular cybercrime commodity
Learn what Certificates as a Service stand for, discover why Code Signing certificates are a precious commodity and find out how to protect yourself online.
USB Killer 2.0 – How to easily burn a PC with a USB device
In March I presented the PoC of a computer-frying Killer USB pendrive designed by the Russian researcher, now the USB Killer 2.0 is arrived!